Gumroad for subscriptions
Gumroad is a lovely product - simple, easy way to sell digital products. Beyond uploading digital products and selling on Gumroad however, another interesting mostly overlooked feature is using it to collect payments outside uploaded digital contents. What this means is that you can use it for your app subscription, one-time fee to sign up for a web app and similar cases. By combining Gumroad's overlay and ping features, something close to a perfect payment solution for your web app can be achieved.
The overlay
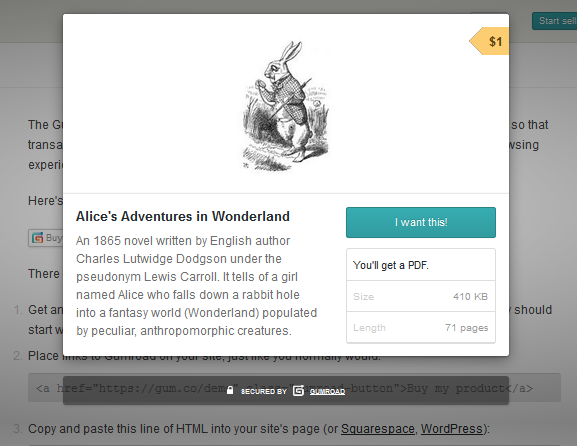
By adding few lines of Javascript to your code, a click on a button or link within your web app can bring up the Gumroad modal window for your product. The whole payment process can then be done within the window.
The Ping
From your Gumroad developer settings, you can set a ping endpoint (a url) where Gumroad sends details of every purchase. (You can see details of the parameters that are sent at gumroad.com/ping). You can then match the payment email with that in your database and upgrade the user as necessary. As Gumroad allows you request additional data in the payment form, another way is to request the payer's username within the payment form. Once the ping is sent, you can then match that against your db.
Cons
- This doesn't count as a con, but so you know, you should be SSL enabled to use Gumroad overlay
- Gumroad pays out via paypal. So you should have a paypal account or a friend who does and can easily transfer the money to you.
- You must keep your ping endpoint confidential and unguessable to prevent fake pings from different source. I'd expect Gumroad to give devs a unique token that is then sent along ping parameters. Devs can use that to verify the authenticity of pings at their ends.